

 The learning objective of this lab is for students to gain the first-hand
experience on format-string vulnerability by putting what they have learned
about the vulnerability from class into actions.
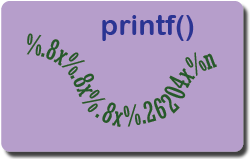
The format-string vulnerability is caused by code like
printf(user_input), where the contents of variable
of user_input is provided by users. When this program is running
with privileges (e.g., Set-UID program or server program),
this printf
statement becomes dangerous, because it can lead to one of the following
consequences: (1) crash the
program, (2) read from an arbitrary memory place, and (3) modify
the values of in an arbitrary memory place. The last consequence
is very dangerous because it can allow users to modify internal
variables of a privileged program, and thus change the behavior
of the program.
The learning objective of this lab is for students to gain the first-hand
experience on format-string vulnerability by putting what they have learned
about the vulnerability from class into actions.
The format-string vulnerability is caused by code like
printf(user_input), where the contents of variable
of user_input is provided by users. When this program is running
with privileges (e.g., Set-UID program or server program),
this printf
statement becomes dangerous, because it can lead to one of the following
consequences: (1) crash the
program, (2) read from an arbitrary memory place, and (3) modify
the values of in an arbitrary memory place. The last consequence
is very dangerous because it can allow users to modify internal
variables of a privileged program, and thus change the behavior
of the program.
In this lab, students will be given two containers, each running a server program that has a format-string vulnerability. Their job is to develop schemes to exploit the vulnerability on these servers, and eventually gain a root shell on them.
| Please give us your feedback on this lab using this feedback form. | |
| The SEED Labs project is open source. If you are interested in contributing to this project, please check out our Github page: https://github.com/seed-labs/seed-labs. |