

 The learning objective of this lab is for students to gain the first-hand
experience on buffer-overflow vulnerability by putting what they have learned
about the vulnerability from class into actions.
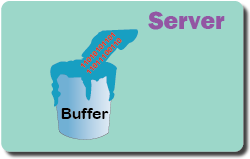
Buffer overflow is defined as the condition in which a program attempts to
write data beyond the boundaries of pre-allocated fixed length buffers. This
vulnerability can be utilized by a malicious user to alter the flow control of
the program, even execute arbitrary pieces of code. This vulnerability arises
due to the mixing of the storage for data (e.g. buffers) and the
storage for controls (e.g. return addresses): an overflow in the data part can
affect the control flow of the program, because an overflow can
change the return address.
The learning objective of this lab is for students to gain the first-hand
experience on buffer-overflow vulnerability by putting what they have learned
about the vulnerability from class into actions.
Buffer overflow is defined as the condition in which a program attempts to
write data beyond the boundaries of pre-allocated fixed length buffers. This
vulnerability can be utilized by a malicious user to alter the flow control of
the program, even execute arbitrary pieces of code. This vulnerability arises
due to the mixing of the storage for data (e.g. buffers) and the
storage for controls (e.g. return addresses): an overflow in the data part can
affect the control flow of the program, because an overflow can
change the return address.
Activities: Students will be given four different servers, each running a program with a buffer-overflow vulnerability. Their task is to develop a scheme to exploit the vulnerability and finally gain the root privilege on these servers. In addition to the attacks, students will also experiment with several countermeasures against buffer-overflow attacks. Students need to evaluate whether the schemes work or not and explain why.
| Please give us your feedback on this lab using this feedback form. | |
| The SEED Labs project is open source. If you are interested in contributing to this project, please check out our Github page: https://github.com/seed-labs/seed-labs. |